Securing Communication using Cryptography
Cryptography has numerous applications but the most basic is its use in securing an insecure communication channel. In this section, this common use-case is detailed using a symmetric key cryptographic scheme.
Consider three users, Alice, Bob, and Oscar. Alice wishes to communicate with Bob privately but the channel between them is unfortunately insecure. Generically speaking this channel could be an Internet-based communication link, telephone lines, WiFi or even a cellular phone network. Oscar is a curious user who wants to listen in to Alice and Bob's conversation (see figure below).
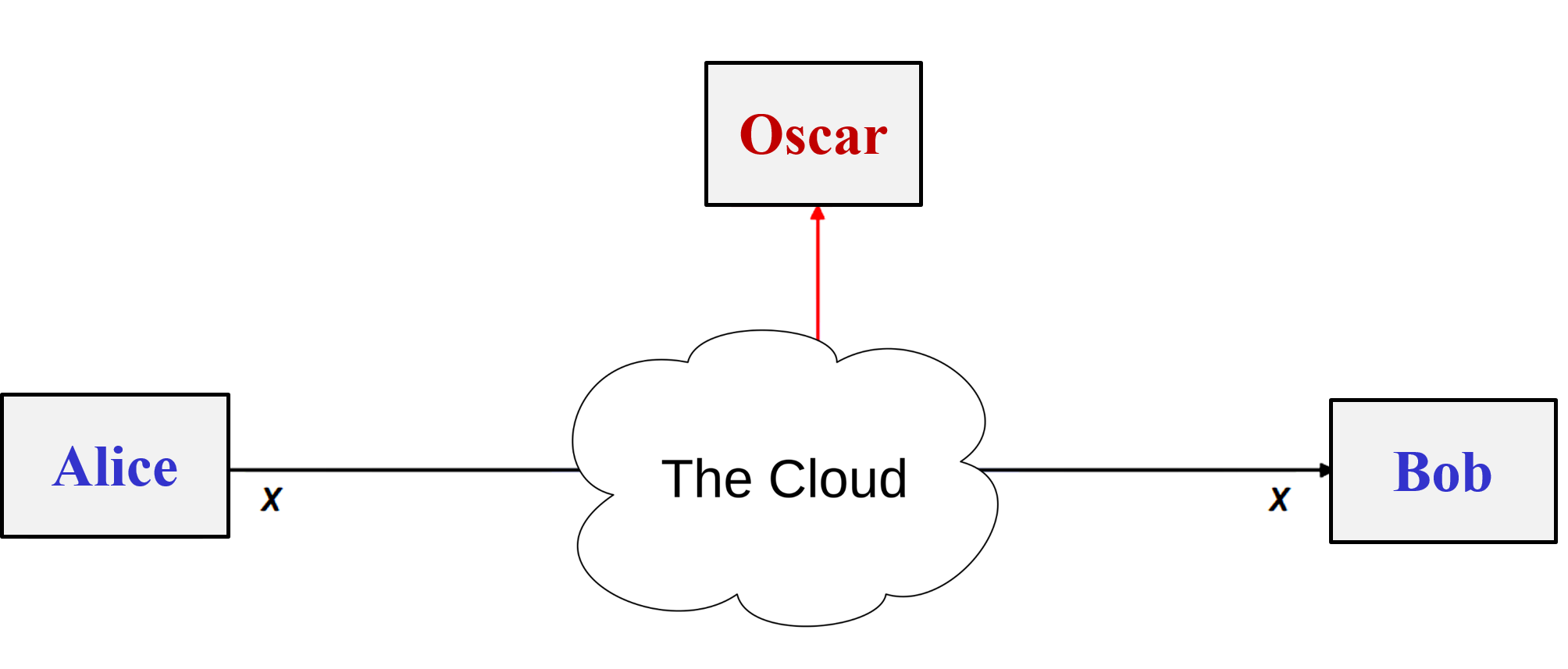 Communication over an insecure channel
Communication over an insecure channel
Oscar is able to listen in to the channel in an authorized way (also called an eavesdropping attack) because he has access to the channel. This means he has access to the router in case of Internet-based communication or simply is monitoring the radio signals as in case of Wi-Fi communication. This common situation applies to any scenario where two or more communicating parties are sharing data that is of some worth to someone else. Examples of such data could be for example financial secrets, business plans or political decisions not yet shared with the public
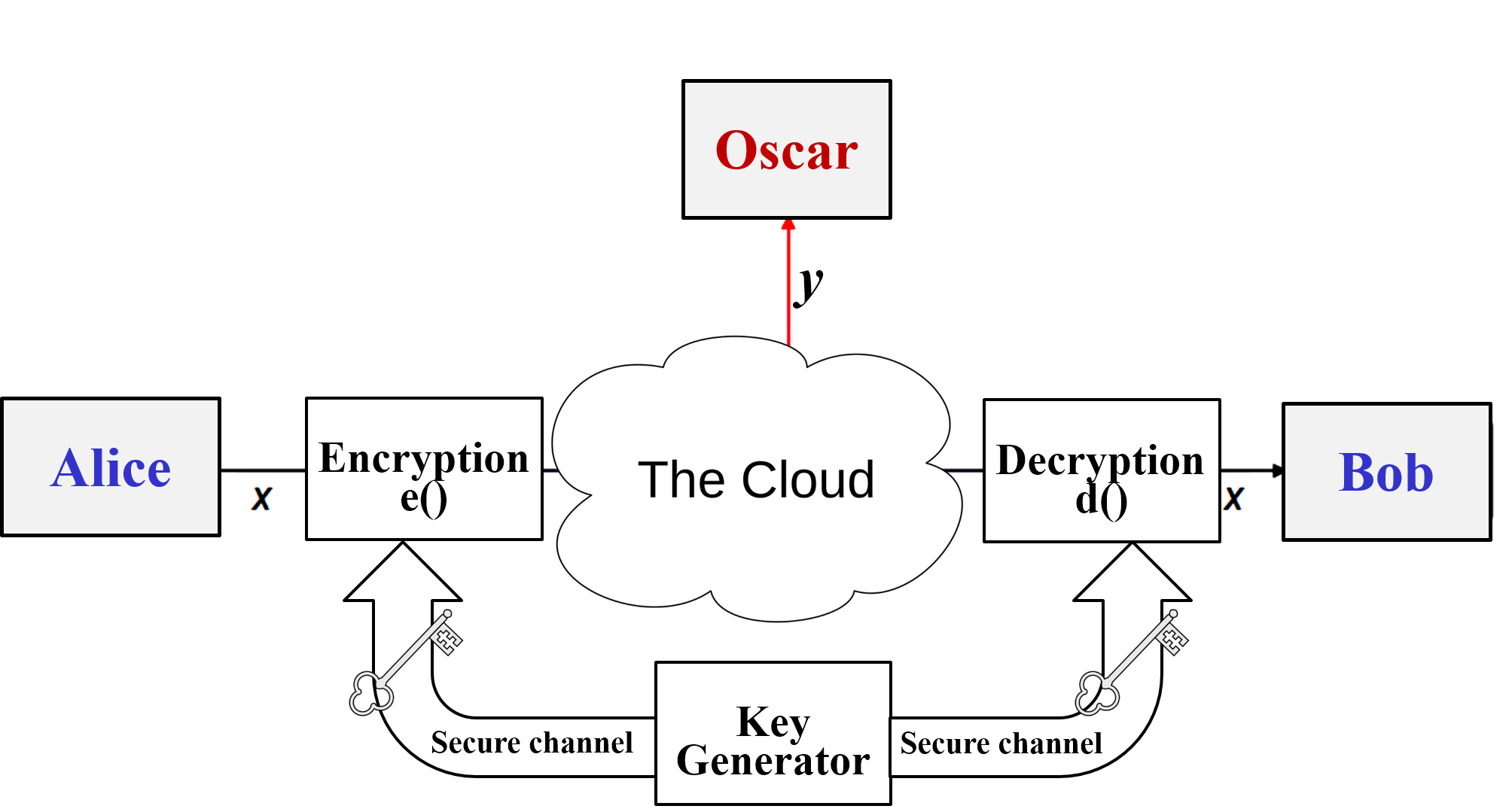 Symmetric-key cryptosystem
Symmetric-key cryptosystem
A cryptosystem built upon Symmetric cryptography provides an elegant solution in this regard. Using such a system Alice uses a symmetric algorithm to encrypt her message $x$, resulting in the ciphertext $y$. When Bob gets this ciphertext he performs a decryption operation on this message accordingly. The decryption and encryption operations are inverse processes of each other (see figure above). The obvious benefits to this assuming that the cipher algorithm itself is strong is that $y$ appears to random bits to an attacker like Oscar and he would not be able to extract any useful information from the communicated data.
A Cryptosystem
We used the terms $x$, $y$ and $k$ to explain the figure above but in fact, they hold a special meaning in cryptography:
A cryptosystem can be defined as a tuple of 5 elements namely $(E, D, X, K, Y)$. $X$ refers to all the plaintexts that this system can consume, the set of keys is referred to as $K$, $Y$ is accordingly the ciphertexts set, $E: X \times K \rightarrow Y$ is the set of cipher algorithms, and finally, $D: Y \times K \rightarrow X$ is the set of deciphering algorithms.
Kerckhoff's Principle
In the 19th century, a renowned cryptographer by the name of Auguste Kerckhoffs stated that a cryptosystem should be secure even if everything about the system, except the key, is public knowledge. This later become widely recognized as the "Kerckhoff's Principle" and became widely embraced by cryptographers.
Kerckhoffs's principle was reformulated by Claude Shannon who asserted that "the enemy knows the system". This design principle states that systems should be designed with the expectation that the attacker will instantly acquire complete knowledge about them. This reformulation is also called Shannon's maxim. The idea is that if the designer bases the security on the fact that the user is ignorant of the system's internal structure then an expert user can break the security mechanism. This concept is also called by some as "security through obscurity".
Since cryptography is a highly mathematical subject, companies that rely on cryptography for protection of customer or employee records tend to try and hide the algorithms they use. History has repeatedly proved that this practice doesn't improve the strength of the system's security. In fact, it tends to provide a false sense of security to a system that in reality has a weak implementation. This is especially true with state-of-the-art technologies today such as virtualization which makes it possible to easily reverse engineer software and their underlying algorithms.
Note that keeping the algorithm secret is not the same as keeping the cryptographic keys secret. The latter will not break Kirchoff's principle. In fact, keeping the keys in a safe and secure place is a good security practice.
- Based on the definition of a cryptosystem write down the 5-tuple representation of the following ciphers:
- Julius invents a new cipher which takes as plaintext input a string of alphabets (A through Z) and replaces each letter in the plaintext with another letter some fixed number of positions down the alphabet. For example, with a left shift of 3, D would be replaced by A, E would become B, and so on.
- ROT-13 takes as plaintext input a string of alphabets (A through Z) and replaces each one by the letter 13 places further along in the alphabet, wrapping back to the beginning if necessary. A becomes N, B becomes O, and so on up to M, which becomes Z, then the sequence continues at the beginning of the alphabet.
- (Socrative option available: Overview of a cryptosystem) Consider the following scenario:
BestBank.com has set up an e-banking system. Customers connect to the banking server. The customer authenticates using either a password or a certificate and private key generated by an application from BestBank.com. Once the customer is authenticated against the banking server, he can view and update his account information. The client's access rights are checked on every transaction. BestBank.com hired a cryptographer to design a new encryption scheme that can be used to ensure the confidentiality and integrity of data communicated between the client and the server. It is keeping the information about the new algorithm secret to limit the information available to the attacker.
- Which cryptographic design principles does this scenario violate?
- How does this violation affect the security of the system?
- How would you change the design to make it follow the design principle?