Cryptography
According to Encyclopedia Britannica, cryptography is defined as:
"Practice of enciphering and deciphering of messages in secret code in order to render them unintelligible to all but the intended receiver."
In short, cryptography is the science of sending secret messages. People have been communicating using secret messages for thousands of years. Soldiers in the field use them so the enemy won’t figure out their battle plans; friends use them when they want to keep their notes private; and, in the modern day, people shopping on the Internet use them to keep their bank card numbers secret.
The commonly used term “secret code” refers to the method for changing a message into a secret message. A very simple secret code was used in Boston in 1776 to communicate a message to Paul Revere about how the British were coming. The code was based on the number of lanterns hung in the church bell tower: “One if by land, two if by sea.”
 The Old North Church at Boston, North End was the place from where the "One if by land, two if by sea" signal is reported to have been sent. (source: www.destination360.com/north-america/us/massachusetts/boston/old-north-church)
The Old North Church at Boston, North End was the place from where the "One if by land, two if by sea" signal is reported to have been sent. (source: www.destination360.com/north-america/us/massachusetts/boston/old-north-church)
Applications
Cryptography plays a role in everything ranging from secure online payment systems and social media applications to smartphones, ATMs, automobiles and even health care implants. The Allies code-breaking efforts of the cryptographic Enigma machine used by the Germans during world war II is said to have changed the tide of the war. More recently we are witnessing even more promising use cases for cryptography like the blockchain for documenting data on the Internet and vehicle-to-vehicle communications. This is in stark contrast to the past, where cryptography was exclusively used by the government and military for secure communications or by financial institutions for storing account information. Due to the use of crypto-algorithms in every walk of life, every Information Technology user needs to be familiar with how cryptography works and its practical applications.
 Everyday applications of cryptography
Everyday applications of cryptography
Unfortunately, cryptography can be used for bad as well as for good. Among other reasons such as human error, data breaches due to cryptographic failures or lack of it are dominating headlines in recent years. The figure below depicts the documented cases of records and data breaches that were compromised in the USA from 2005 to 2017. Interestingly, this number has reached the highest figures to date in the year 2017 with approximately 179M records compromised.
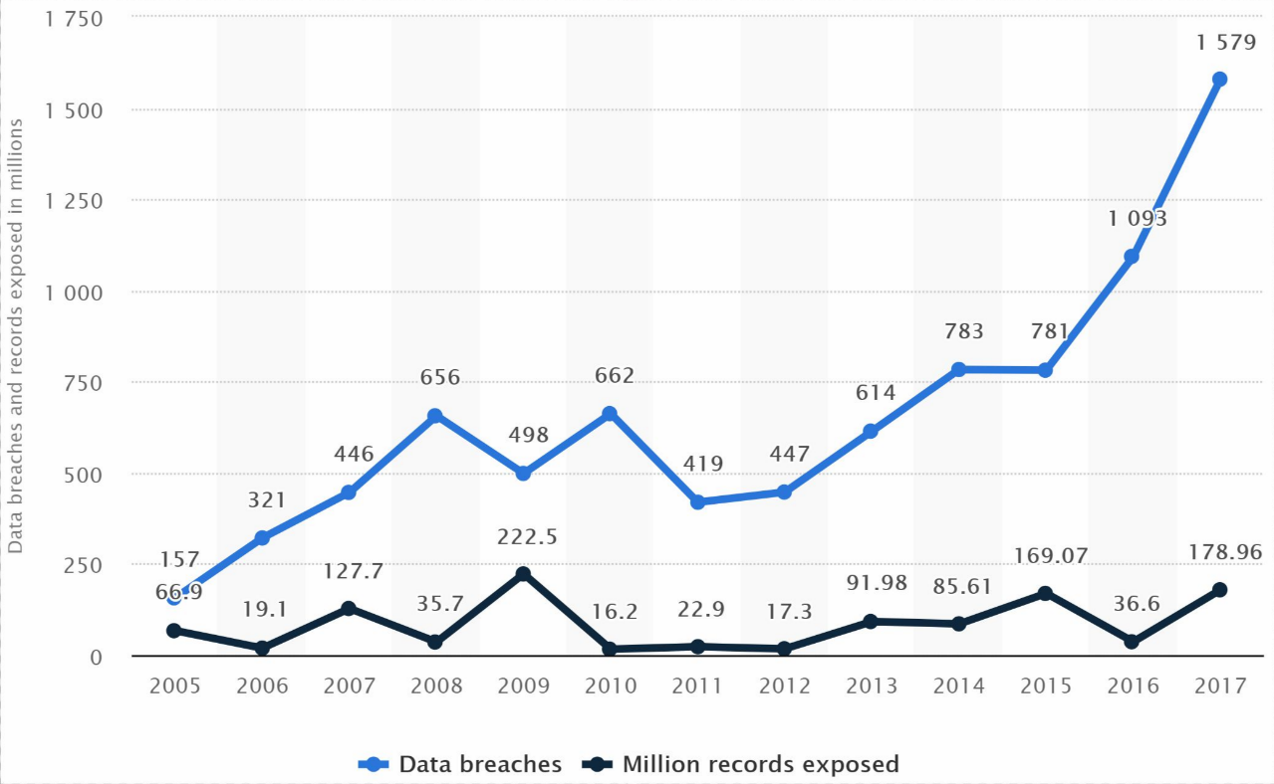 The number of records and data breaches compromised between 2005-2017. (source: statista).
The number of records and data breaches compromised between 2005-2017. (source: statista).
Cryptolocker, Ghost miner, Heartbleed, Wannacry, Backoff are the scary names of some recent software bugs and applications that directly use cryptography for evil purposes.
Cryptology is a cross-cutting discipline encompassing concepts from mathematics, electrical engineering and computer science. It is a highly evolving field, with a rapid pace of development. In the last three decades, cryptography has made advances in theory and there is a much better understanding of security techniques and the manner in which we can prove our algorithms to be secure. In applied cryptography, the world is witnessing advancements with older algorithms being broken and retired and new ones being adopted.
Terminology
In cryptography, the cryptographic algorithm or simply algorithm for short is used to mean a particular type of secret code that changes each letter of a message into another letter or symbol. A system that relies on one or more algorithms to implement a particular security service is called a cryptosystem. Generally, a cryptosystem constitutes algorithms of three main kinds. (1) Algorithms for key generation, (2) for encryption, and (3) for decryption. Keys also called passphrases are parameters of pieces of information that is responsible for the functional output of the cryptographic algorithm and can be of varying sizes. The term cipher is typically employed to indicate a pair of encryption and decryption algorithms.
Classification
A bird's eye view of the field of cryptography can be seen in the figure below.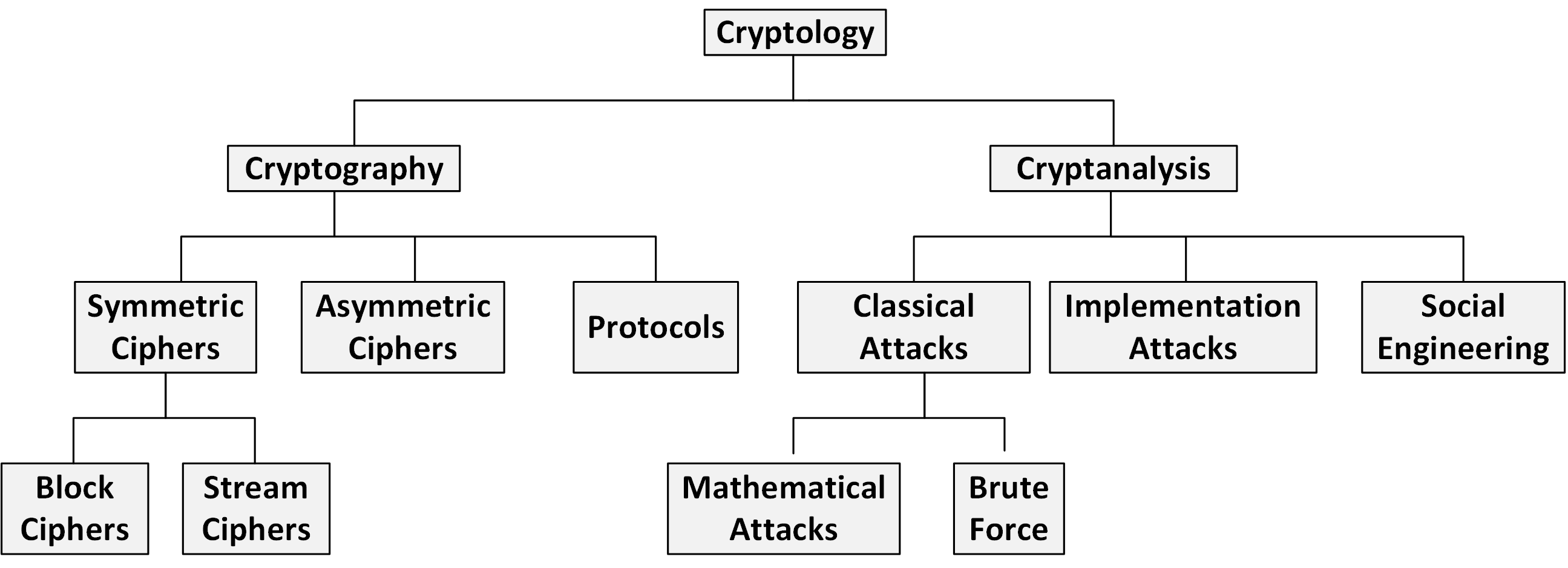 Overview of the field
Overview of the field
Cryptography is a subbranch of cryptology. The other branch is called cryptanalysis. Cryptography refers to the science of writing secrets with the aim of obscuring the message's meaning. The art and science of breaking cryptosystems are referred to as Cryptanalysis.
Cryptanalysis
Cryptanalysis also called code breaking is not just performed by hackers but conducted by cryptanalysts and academic researchers alike. If people who try to break ciphers didn't exist then we would never know whether they are really secure or not. Cryptanalysis is an important part of cryptology because it the sole way to prove that a cryptosystem is secure.
Cryptanalysis can be divided into three main parts: classical, implementation based and social engineering. Classical attacks are further subdivided into mathematical attacks, that attempt to break the underlying mathematics and the cipher's structure and brute-force attacks, which consider the cipher algorithm a black box and enumerate all key combinations for gaining access.
Attacks that target the underlying implementation also called fuzzing look for weaknesses or bugs in the way the cryptosystem has been implemented and typically require physical access to it. Social Engineering attacks are historically the most successful and include techniques such as blackmail, bribe, trickery and espionage to break a cryptosecure system that involves humans.
Cryptography
Cryptography itself is composed of three main branches: Symmetric Algorithms is the most commonly known branch: parties that wish to communicate secretly employ a cipher and share a key to make that work. Symmetric cryptography was the only type known and employed throughout history up until 1976. It still popular today for bulk data encryption and ensuring the integrity of messages.
Asymmetric cryptography is also known as public key cryptography is another kind of cipher invented in 1976 by Whitfield Diffie, Martin Hellman, and Ralph Merkle. In Asymmetric cryptography, a communicating party employs not just one but two keys. There exists a secret keyjust like that in symmetric cryptography but also another key, known as a public key. Public key cryptography is important for security services such as key establishment, digital signatures and, classical data encryption.
Cryptographic Protocols are the application of cryptographic algorithms. Public key, as well as symmetric algorithms can be viewed as building blocks for constructing cryptosystems, for example, secure network communication. Transport Layer Security (TLS) a security protocol employed in all Web browsers, is one such cryptographic protocol. The third subbranch of cryptographic algorithms is hash functions however we will discuss them with symmetric ciphers because they share some common properties.
In most practical applications that employ cryptography, a combination of symmetric, asymmetric and hash functions can be found. The reason for these hybrid schemes is that each family of algorithms has its own specific strengths and weaknesses and using them together usually leads to a robust solution.
Cryptographic Considerations for Secure System Design
It is important to note that cryptography is a building block for our security approach and is not the ultimate solution to all security problems. Cryptography is only one aspect of cyber-security and there exist many other aspects of building a cryptosystem.
Cryptography under many conditions builds upon some algorithms. History has shown that when people design crypto algorithms that think it is safe. However several years later it turns out that the algorithm made certain assumptions rendering it unsafe and in turn breaking all cryptosystems that rely on it. Furthermore, even if an encryption algorithm can be proved to be safe and it is shown that breaking the algorithm is beyond the computation capability know to man, eventually the algorithm needs to be translated into a computer program to be used in a cryptosystem. It is well known that when people implement code they are prone to embed bugs due to human error. One could end up using an insecure implementation of a secure cryptographic algorithm.
Last but not least the reason we say that cryptography is only a building block to implement security is that there exists no one-size-fits-all cryptographic solution. Instead, the solution must be tailored to the problem. Consider the domain of car manufacturing. If you buy the most expensive parts from factories and put them together to build the perfect car you may still not have the best car in the world. The reason being that one has to put the right part in the right place. The best or most expensive parts assembled in the wrong way will not give one the best car. It is the same rationale for cryptography. One can pick different components to build a security approach to make sure that critical information and infrastructure is secure. However, one would want the best or most feasible components and not the most expensive.
Consider the matter of choosing a particular key size in a cryptographic algorithm. One cannot say that a 2048 bit key will always be safer than a 1024 bits key. If the cryptographer is going to be using this algorithm to design a cell phone with limited computing power it may not be able to handle that large a key size.
- Write down three modern applications of cryptography not discussed in the notes.
- What could possibly be an abuse of cryptography?
- A cryptographer once stated that cryptography could provide complete security and that any other computer security controls were unnecessary. Why is he wrong? (Hint: Think of an implementation of a cryptosystem, and ask yourself what aspect(s) of the implementation can cryptography not protect.)
- (Socrative option available: Introduction to Cryptography) Some functionalities that cryptographic algorithms provide are (Confidentiality, Authentication, Integrity, and Non-repudiation). Give a real-world example of each of these functionalities.